Why MFA doesn’t stop phishing becomes clear when you understand how attackers target sessions instead of passwords.
Intro
Why MFA doesn’t stop phishing is one of the most misunderstood problems in modern cybersecurity.
Most security teams still operate under an outdated assumption:
password + MFA = secure account
That model no longer matches how modern identity attacks work.
MFA still helps against credential stuffing, password reuse, and basic account takeover. But attackers have adapted. They no longer need to defeat authentication in the old sense. Increasingly, they target the user during the login flow, the session after the login flow, or the trust model surrounding both.
The result is simple but uncomfortable:
MFA often protects the login challenge, not the authenticated state that follows it.
That distinction matters because the real asset in modern cloud environments is no longer just the password. It is the authenticated session: the token, the cookie, the trusted state that survives after the prompt is gone.
If your security model stops at “MFA enabled,” you are defending the wrong layer.
This is exactly why MFA doesn’t stop phishing in many real-world attacks.
The diagram below shows exactly how modern phishing bypasses MFA by targeting the session layer.
Why MFA Doesn’t Stop Phishing in Modern Identity Systems
The Core Mistake: Treating Identity as a Login Event
Many organizations still think of authentication as a single event. A user enters credentials, completes a second factor, and gets access.
That is no longer how identity works in practice.
Modern identity is a chain:
authentication → token issuance → session establishment → reuse → refresh → policy reevaluation
MFA protects only one point in that sequence. Everything after it depends on how well the platform protects sessions, evaluates context, enforces device trust, and reacts to risk.
This is the core strategic mistake in modern identity security:
teams protect the login, but attackers target the trusted state created by the login.
Why MFA Solved Yesterday’s Problem
MFA was designed for a different threat model.
The old problem looked like this:
- attacker steals a password
- attacker attempts login
- second factor blocks access
- attack fails
Against that model, MFA was and still is a strong improvement over password-only security.
But identity systems evolved. Cloud services, SaaS platforms, federated sign-in, OAuth, OpenID Connect, SAML, session cookies, access tokens, and refresh tokens changed the attack surface.
The attacker’s goal shifted from:
“Can I steal the secret?”
to:
“Can I obtain or replay a valid identity state?”
That is a much more dangerous problem, because a valid session can let an attacker operate as the user without needing to challenge MFA again.
Where MFA Actually Breaks
1. Authentication Is Not the Same as Session Trust
MFA protects the challenge.
It does not automatically protect what the system issues after the challenge succeeds.
Once a service grants:
- session cookies
- access tokens
- refresh tokens
the security question changes. If those artifacts are stolen, replayed, or reused from another context, the service may continue to treat the attacker as legitimate.
That is why many identity breaches today are not about defeating MFA directly. They are about abusing what happens after MFA succeeds.
2. Tokens Are the Real Keys in Modern Environments
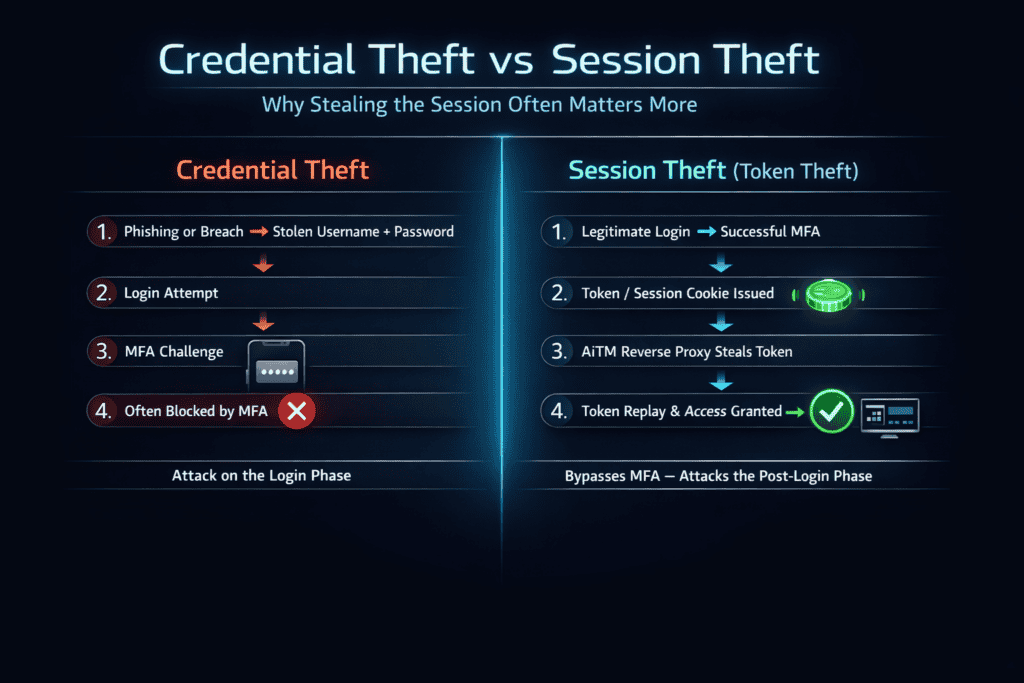
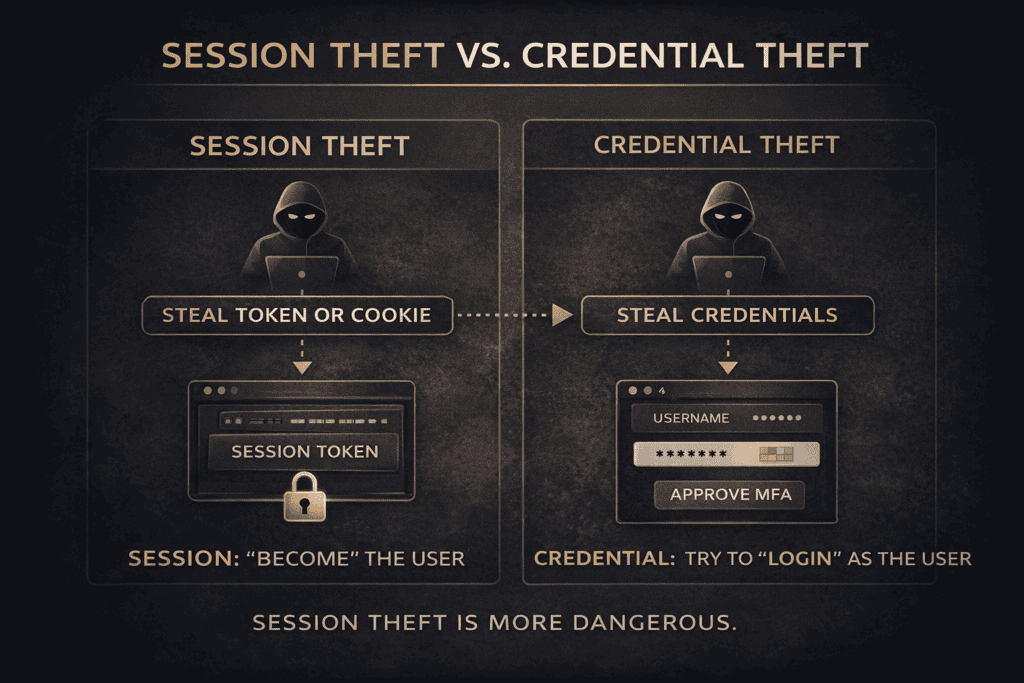
The diagram below shows the difference between session theft and credential theft in modern identity attacks.
In Microsoft 365, Google Workspace, Slack, Salesforce, and similar platforms, access is often governed by tokens and sessions rather than by the password itself.
That means:
steal the token, and you may effectively become the user
This is what makes session theft more dangerous than classic credential theft. The attacker is not trying to guess or crack authentication. The attacker is stepping into an already trusted state.
3. Trust Often Persists Too Long
Many organizations still allow sessions to remain valid too long, refresh silently, or avoid meaningful re-evaluation unless the token naturally expires.
That creates operational space for attackers.
An account owner may change the password, suspect something is wrong, or even sign out in one location, while a stolen session remains usable elsewhere. If risk-based reevaluation is weak, the attacker keeps the benefit of the earlier trust decision.
4. The User Remains Inside the Security Boundary
Push approvals, codes, and interactive login prompts all assume the user can reliably make safe decisions in real time.
In reality, users are:
- busy
- conditioned by repetitive prompts
- overloaded by email and app notifications
- operating on mobile devices
- trained to move quickly
Modern phishing exploits exactly that environment.
Attackers do not always need to beat the user. Sometimes they only need the user to cooperate at the wrong moment.
5. Weak Fallback Paths Undermine Strong Primary Controls
A company may deploy security keys or passkeys and still leave open:
- SMS fallback
- insecure recovery email flows
- helpdesk override procedures
- legacy authentication protocols
- unmanaged device exceptions
At that point, the environment is not protected by its strongest control. It is exposed through its weakest allowed route.
The Real Attack Paths That Bypass Traditional MFA
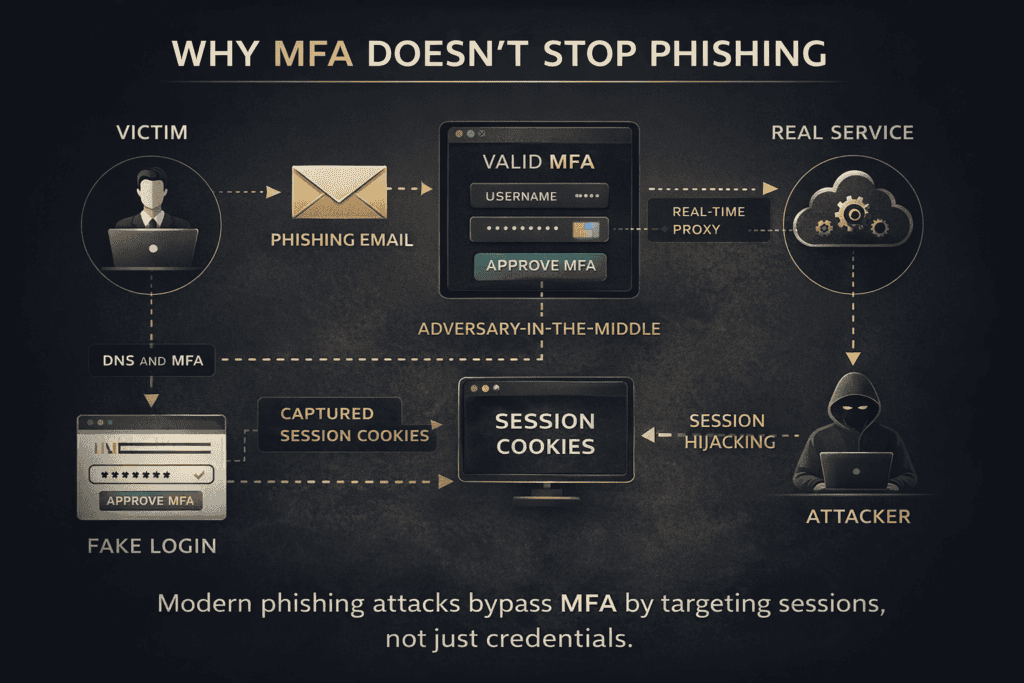
Adversary-in-the-Middle (AiTM) Phishing
This is one of the most important identity attack patterns today.
In an AiTM flow:
- the victim clicks a phishing link
- the phishing site acts as a reverse proxy between the victim and the real service
- the victim enters credentials
- the victim completes MFA on the legitimate service through the proxy
- the attacker captures the authenticated session
- the attacker reuses that session
This is the hard truth many teams still resist:
MFA can work exactly as designed and the organization can still lose.
The problem is not always failed authentication. The problem is successful authentication being captured and repurposed.
This is the core reason why MFA doesn’t stop phishing when attackers use AiTM techniques.
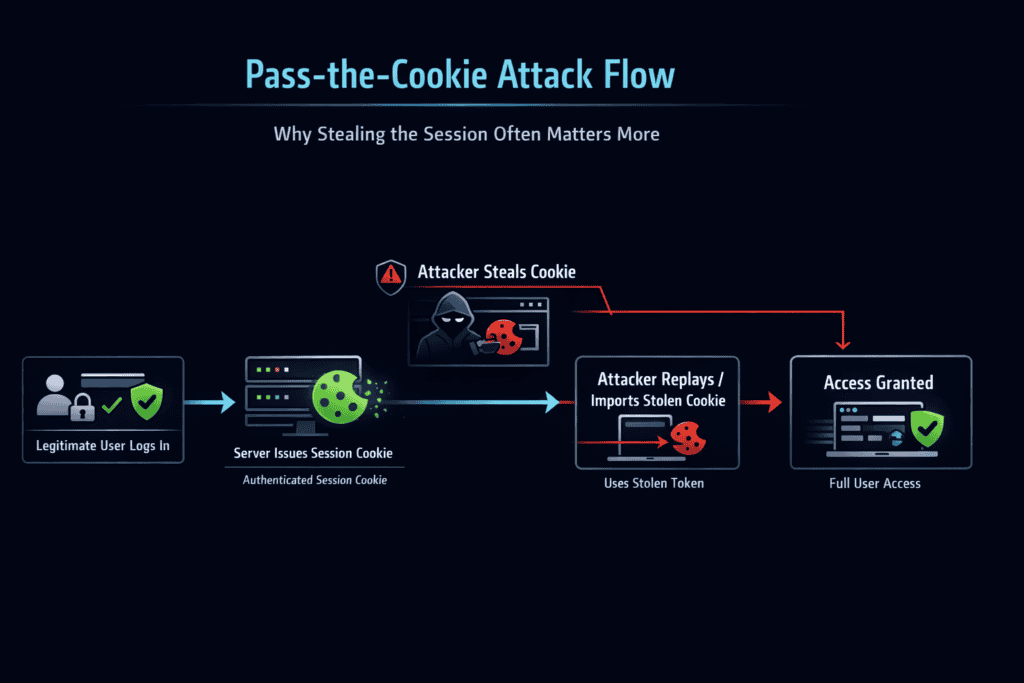
Session Hijacking
In some attacks, the phishing page is not even the main issue.
If an attacker gets hold of a valid session cookie or token, they may bypass the entire authentication process and operate directly inside the user’s session context.
This is post-authentication compromise, and it is exactly why login-centric defenses are no longer enough.
Push Fatigue and Approval Abuse
Not all MFA bypasses are technically advanced.
Some are brutally simple:
- flood the user with push prompts
- pretend to be IT support
- create urgency
- tell the user to approve “to fix the issue”
The weakness here is not cryptography. It is workflow manipulation.
OAuth Consent Phishing
Some attacks do not try to steal credentials at all.
Instead, the victim is tricked into authorizing a malicious or overprivileged application. Once granted consent, that application may gain persistent access to data, mail, files, or APIs without ever needing the password.
In these cases, “MFA enabled” is largely beside the point.
Legacy Authentication and Weak Recovery
Older protocols, weak password reset processes, unmanaged devices, and insecure exception handling remain common attack paths.
Security teams often celebrate strong frontline controls while leaving side entrances open.
Attackers notice that immediately.
The Real Shift: From Credentials to Identity State
The old mental model was simple:
steal password → gain access
The new model is more accurate:
obtain valid identity state → operate as the user
That identity state may include:
- an authenticated session
- valid access or refresh tokens
- a trusted device context
- an approved OAuth application
- a low-risk sign-in posture in the identity provider
This is why identity defense now has to move beyond passwords and beyond the login screen.
The real perimeter is no longer static authentication.
It is dynamic session integrity.
Why Traditional Security Awareness Falls Short
Most awareness programs still teach users to:
- avoid suspicious links
- check for spelling mistakes
- look at the sender address
That is not enough against modern phishing.
Today’s attacks are often:
- visually convincing
- contextually relevant
- timed to business processes
- proxied through realistic login flows
- designed to exploit approval habits, not obvious mistakes
The skill users actually need is more advanced:
they must know when not to approve identity-related actions, even when the flow feels familiar.
Security awareness has to evolve from “spot the typo” to recognizing abnormal identity workflows under pressure.
Why MFA Feels Safer Than It Sometimes Is
There is a dangerous psychological effect here.
When a user sees:
- a familiar Microsoft or Google login flow
- a real MFA prompt
- a successful sign-in
they often interpret that as proof of legitimacy.
But in an AiTM attack, the attacker is relaying that exact flow in real time.
That means MFA can become, in the user’s mind, a false signal of trust rather than a reliable signal of safety.
This does not mean MFA is useless.
It means traditional MFA is often context-blind.
It verifies that a factor was completed. It does not always verify that the authentication request is happening in the right place, on the right origin, under the right conditions.
What Actually Works
1. Use Phishing-Resistant Authentication
The strongest structural improvement is to adopt:
- FIDO2 security keys
- passkeys
- device-bound cryptographic authenticators
These methods are stronger because they use origin binding and asymmetric cryptography. The private key stays on the device, and the authentication response is tied to the legitimate domain.
That sharply reduces the value of proxy-based phishing because the attacker cannot simply relay or replay the authentication on another origin.
This is not just “better MFA.”
It is a different security property.
2. Enforce Device and Context Trust
Authentication without context is weak.
A stronger model asks:
- is this a compliant device?
- is the browser trusted?
- does the location make sense?
- is the sign-in risky?
- is the user’s behavior consistent?
- should this session exist under these conditions?
This is where Conditional Access, device compliance, managed browsers, and risk-based policies become critical.
3. Reevaluate Trust Continuously
A session should not remain trusted simply because it was once established successfully.
Continuous reevaluation matters because risk changes over time.
A user account may become high risk. A token may appear in a suspicious context. A session may suddenly behave differently from its baseline.
If reevaluation is slow, attackers keep access longer than they should.
If reevaluation is fast, dwell time shrinks.
4. Treat Tokens as High-Value Secrets
Many teams still protect passwords more seriously than tokens.
That is backwards.
In modern cloud identity, tokens are temporary keys to systems, data, and workflows. They should be protected, bounded, monitored, and invalidated aggressively when risk changes.
5. Detect Abuse After Authentication
A major failure in many programs is that visibility drops after login succeeds.
That is the wrong point to stop watching.
Teams need detection for:
- unusual session reuse
- mailbox rule manipulation
- abnormal API behavior
- suspicious OAuth consent activity
- unusual access patterns after sign-in
- token reuse from unexpected contexts
The breach often becomes visible only after authentication is complete.
6. Eliminate Weak Fallbacks
Strong identity systems cannot coexist comfortably with weak recovery and legacy exceptions.
If you allow phishable fallback methods, attackers will route around your best control.
This is why many identity hardening projects fail. The organization deploys something strong, then preserves enough weak exceptions to keep the overall environment exposed.
7. Build Real Identity Incident Response
A password reset is not enough for a modern identity compromise.
Effective response may require:
- global session revocation
- token invalidation
- mailbox rule review
- OAuth application audit
- device posture review
- sign-in log analysis
- consent and persistence investigation
Identity incidents are not isolated events. They are distributed trust failures across time, devices, sessions, and services.
The Strategic Reality
MFA is not broken.
The problem is that many organizations treat MFA as the end of the identity conversation when it is only one control inside a much larger trust system.
That is the real failure:
an incomplete identity model disguised as a mature security posture
The Hard Truth in One Sentence
MFA does not protect your account as a whole.
It protects a single moment in the authentication flow.
Modern attackers increasingly target:
- the user during the flow
- the session after the flow
- the trust model around the flow
That is why checkbox MFA is not enough.
What This Means for Security Leaders
If your message is still:
“We enabled MFA, so we are covered”
you are behind the current threat model.
If your strategy is:
- phishing-resistant authentication
- session governance
- device trust
- continuous reevaluation
- post-authentication detection
- hard recovery architecture
then you are defending identity at the level where modern attacks actually happen.
That is the difference between compliance language and operational reality.
Move Beyond Checkbox MFA
Understanding why MFA doesn’t stop phishing is critical for modern identity security.
Modern phishing does not stop at the login page. Your defenses should not stop there either.
If you want a serious view of your exposure, the right question is not “Do we have MFA?”
The right question is:
Can an attacker still obtain, replay, or persist a trusted identity state in our environment?
That is where real identity security starts.
Book an Identity Architecture Review
If your organization runs on Microsoft 365 or Microsoft Entra ID, we can map the identity attack surface that traditional MFA leaves behind.
The review focuses on:
- AiTM exposure
- token and session risk
- Conditional Access gaps
- fallback weaknesses
- identity recovery blind spots
You get a prioritized hardening view based on real attack paths, not generic compliance talk.
[Schedule Your Review →]
Link this article to:
- What Is AiTM Phishing and Why It Beats Traditional MFA
- Passkeys vs MFA Apps: What Actually Changes
- Why Session Cookies Matter More Than Your Password
- How Conditional Access Shrinks the Damage of Identity Attacks
- Why “MFA Enabled” Is a Weak Security KPI