Session vs credential theft is no longer a theoretical distinction. It is the defining shift in modern identity attacks.
Most security teams still focus on protecting login.
Strong passwords. MFA. Reset flows.
But attackers have adapted.
They no longer break in.
They steal the trust issued after login.
According to Microsoft’s Digital Defense Report, adversary-in-the-middle phishing attacks are rapidly increasing as attackers shift toward session token theft. Meanwhile, OWASP and MITRE ATT&CK confirm the same reality: once a session token is stolen, authentication no longer matters.
This is where most defenses fail.
Table of Contents
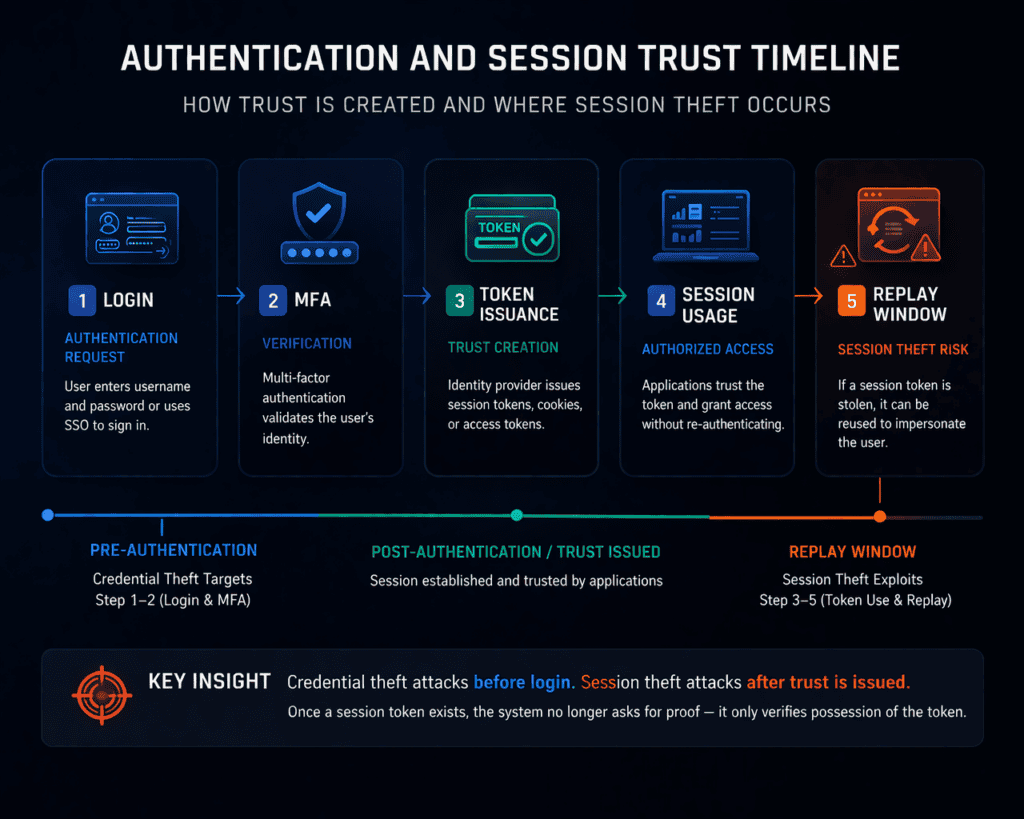
The Trust Timeline Explained
Every identity system follows the same structure:
- Authentication request
User initiates login - Verification
Credentials and MFA validated - Trust issuance
Tokens and cookies are created - Ongoing access
System trusts the session - Replay window
Stolen tokens can be reused
Key distinction:
Credential theft attacks steps 1–2
Session theft attacks steps 3–5
Extra variaties (voor verschillen
Credential Theft vs Session Theft
Credential theft targets login secrets:
- Passwords
- MFA codes
- API keys
- Stored browser credentials
How it happens:
- Phishing pages
- Credential stuffing
- Database breaches
- Keyloggers
- Credential dumping
Real-world flow:
- Credentials stolen
- Login attempted
- MFA triggered
- Attack often blocked
Key reality:
Credential theft gives opportunity, not guaranteed access.
Session Theft vs Credential Theft in Practice
Session theft targets what happens after login:
- Session cookies
- Access tokens
- Refresh tokens
- SSO artifacts
Once stolen, these allow full impersonation.
How it happens:
- AiTM phishing
- Infostealer malware
- Browser compromise
- XSS attacks
- Token replay
Real-world flow:
- User logs in normally
- MFA succeeds
- Token issued
- Token captured
- Attacker reuses it
- Access granted
No password needed
No MFA needed
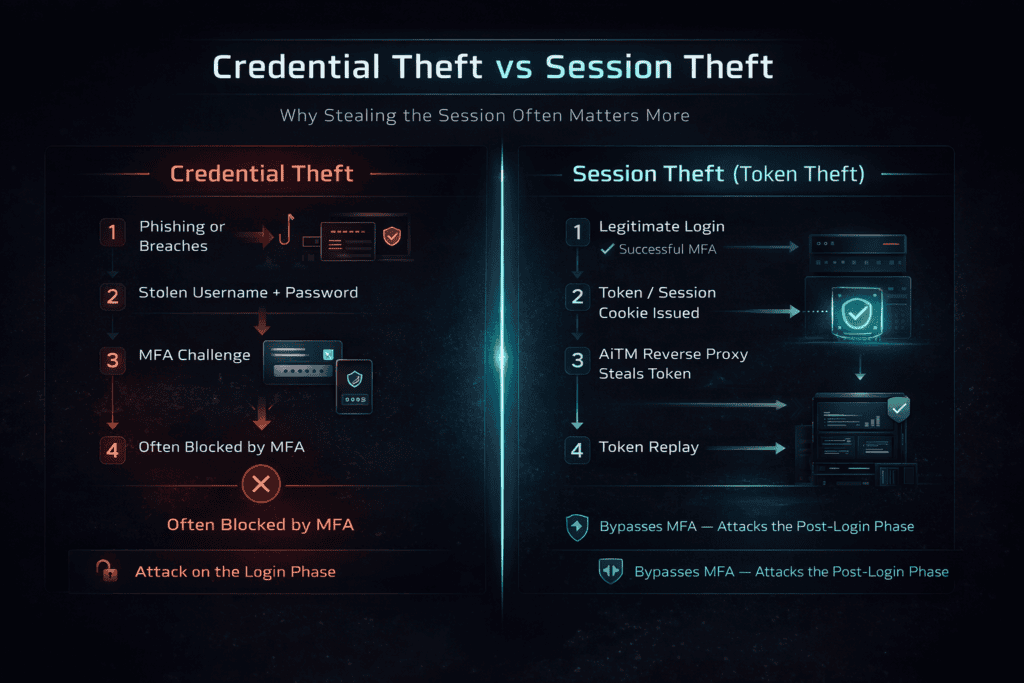
How AiTM Connects Credential Theft and Session Theft
Adversary-in-the-Middle attacks combine both layers.
A reverse proxy sits between the victim and the real service:
- Captures credentials during login
- Captures tokens after login
- Relays everything live
Result:
The attacker gets credentials and active session access.
This is why MFA alone is no longer enough.
👉 Related: AiTM Phishing Explained
Credential Theft vs Session Theft Differences
Target
Credential Theft → login secrets
Session Theft → session tokens
Stage
Credential Theft → pre-authentication
Session Theft → post-authentication
Goal
Credential Theft → login attempt
Session Theft → session reuse
MFA Impact
Credential Theft → often blocked
Session Theft → bypassed
Detection
Credential Theft → visible login anomalies
Session Theft → looks legitimate
Persistence
Credential Theft → until password reset
Session Theft → until token expires
Why Session Theft Is More Dangerous
Attackers follow efficiency.
As defenses improve:
- Passwords get stronger
- MFA adoption increases
- Credential reuse decreases
Attackers shift forward:
From login to session.
Today’s underground markets sell:
- Live session cookies
- Browser fingerprints
- Authenticated sessions
The attack surface has moved.
The System Behind Session Theft
Session theft exists because of system design:
Identity providers
Issue tokens after authentication
Applications
Trust tokens as identity
Browsers
Store tokens locally
Security teams
Measure login, not session
Most dashboards show:
- MFA enabled ✔️
- Password strong ✔️
But ignore:
- token replay
- session anomalies
- device trust
Defense Strategy for Session vs Credential Theft
Defending the Login Layer
- Strong passwords
- Phishing-resistant MFA (passkeys)
- Login anomaly detection
- Credential stuffing protection
Important but insufficient
Defending the Session Layer
Token Binding
Tie tokens to devices
Device Trust
Allow only compliant endpoints
Short Lifetimes
Reduce replay window
Session Monitoring
Detect abnormal behavior
Cookie Hardening
Secure, HttpOnly, SameSite
Endpoint Security
Stop infostealers
Real-World Scenarios
Scenario A Credential Theft
Phishing → login → MFA → blocked
Scenario B Session Theft
Proxy → MFA success → token stolen → access granted
Same user
Same MFA
Different outcome
Bottom Line
Credential theft steals the ability to try.
Session theft steals the proof that access was already granted.
Once trust is issued, most systems stop asking questions.
That is exactly where attackers operate.
CTA Identity Security Upgrade
If your organization relies on Microsoft 365 or Entra ID, you likely have blind spots in your session layer.
Book an Identity Security Review:
- AiTM exposure mapping
- Token replay risk
- Conditional Access gaps
- Session lifecycle weaknesses
Or download:
Identity Hardening Checklist 2026
Can your MFA survive session theft
Internal Linking (Cluster)
Pillar:
How Cyber Attacks Happen
Supporting:
Phishing Attack Explained
Why MFA Doesn’t Stop Phishing
Why Session Cookies Matter More Than Your Password
Next in this Series
Next: Why Session Cookies Matter More Than Your Password
This article will break down how cookies work, why they are a critical weak point, and how attackers exploit them in real environments.