Most people still think the password is the main thing protecting an account.
It is not.
Why session cookies matter more than your password becomes clear the moment you understand what happens after login. Your password only matters at the front door. After authentication, the system shifts trust to something else entirely: the session.
Once a user signs in, the application stops checking the password on every request. It checks whether the browser presents a valid session token.
That changes everything.
Modern attackers don’t always need credentials anymore. If they can steal the active session, they can bypass login, bypass MFA, and inherit access instantly.
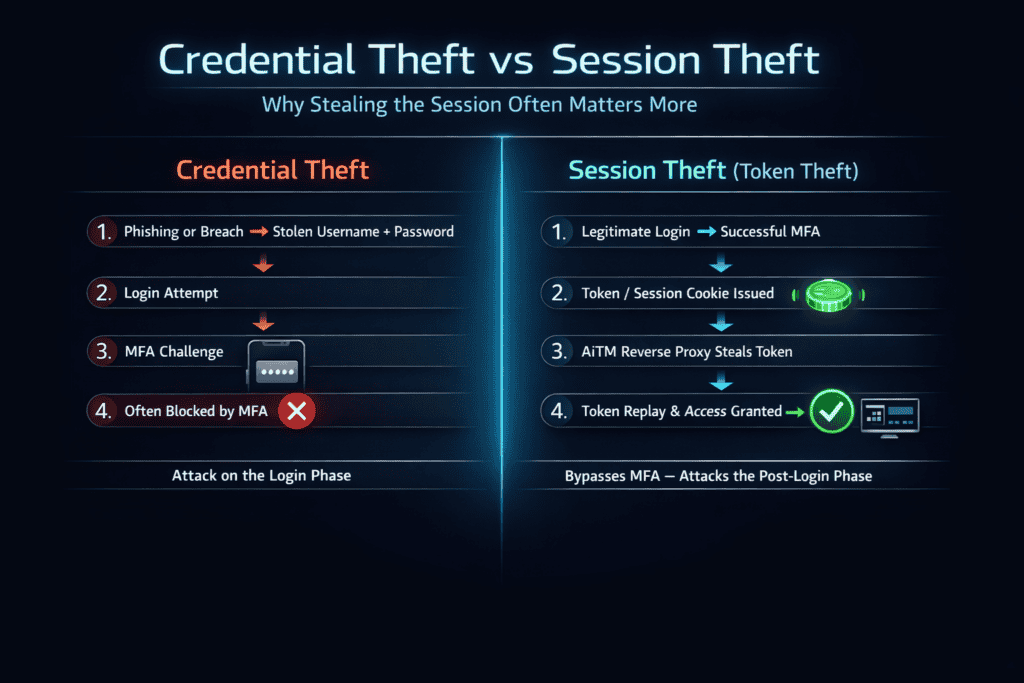
Table of Contents
What a Session Cookie Actually Does
HTTP is stateless. Every request is independent unless the application adds memory.
That memory is the session.
After login, the server issues a session cookie. The browser automatically sends it with every request. The application treats those requests as authenticated.
Key insight:
The password gets you in once.
The session keeps you in.
This is exactly why session cookies matter more than your password becomes a critical concept in modern identity security.
Why Session Cookies Matter More Than Your Password
1. A session cookie can bypass authentication entirely
A password is used to create trust. A session cookie represents trust that has already been granted.
If an attacker steals a valid session cookie, they usually do not need to know the password at all. They also may not need to pass MFA, because MFA was already completed during the original sign-in flow. The attacker simply reuses the authenticated session.
This is what makes session hijacking so dangerous. The attacker is not attacking the login process. They are skipping it.
2. Session theft is often faster than credential theft
Credential attacks usually require one or more steps:
- phishing the victim
- cracking weak passwords
- reusing breached credentials
- bypassing or intercepting MFA
- avoiding login-based detections
Session theft removes much of that work.
If malware, an AiTM phishing proxy, a malicious browser extension, or a browser compromise can extract the active session, the attacker gets immediate usable access. In many cases, that is operationally easier than stealing credentials and then dealing with the controls that sit around th
3. A valid session looks legitimate to the application
That is one of the hardest realities in identity security. Many detections are designed around authentication events such as impossible travel, new-device sign-ins, unusual IP addresses, failed login bursts, or MFA fatigue patterns. But once a request arrives carrying a valid session token, the platform may treat it as normal application traffic.
That makes session abuse quieter than credential abuse.
4. Sessions can remain active for a long time
Many users assume a session lasts only a few minutes. In reality, that is often false.
Modern applications may keep users signed in for days or weeks. Some use refresh tokens, silent reauthentication, or “remember this device” behavior that extends practical access even further. In SaaS environments, that can give an attacker a large post-compromise window.
A stolen password is dangerous. A stolen active session is dangerous right now.
5. MFA protects the login event, not the ongoing session
This is the misunderstanding that causes false confidence.
MFA is valuable. It raises the cost of account compromise and blocks many basic attacks. But MFA does not automatically protect the session that exists after the user signs in. Once the platform has issued a valid session token, possession of that token may be enough to act as the user.
This is exactly why session-based attacks keep growing. Organizations celebrate MFA adoption while attackers move one layer deeper.
6. Modern attackers increasingly target sessions instead of passwords
The industry is slowly learning that identity attacks are shifting from credential collection to session capture.
That shift shows up in several places:
- AiTM phishing kits that proxy the real login flow and steal the post-authentication session
- info-stealer malware that extracts browser cookies and tokens
- malicious browser extensions with excessive permissions
- cloud identity attacks that focus on token replay rather than password guessing
The logic is simple. Stronger passwords and wider MFA deployment made direct credential abuse harder
7. The session is the real operational identity layer
Security teams often talk about identity as if it begins and ends with passwords, MFA apps, or passkeys.
That is incomplete.
Operationally, the session is what the application trusts on each request. That makes session management one of the most important and most underestimated layers in account security. If the session is weak, poorly scoped, too long-lived, or easy to steal, then the strength of the password matters much less than people think.
How Session Cookie Theft Actually Happens
Understanding this attack surface is essential to grasp why session cookies matter more than your password in real-world breaches.
Session cookie theft does not require one single technique. It can happen through multiple attack paths, and that is what makes it dangerous.
AiTM Phishing
Reverse proxy attacks capture sessions after MFA.
How Cyber Attacks Happen: Step-by-Step Breakdown
What Is AiTM Phishing and Why It Bypasses MFA
In an adversary-in-the-middle phishing attack, the victim is lured to a phishing site that sits between them and the legitimate service. The victim enters credentials, completes MFA, and the real site issues a valid session. The phishing proxy captures that session token and hands it to the attacker.
The attacker never needs to defeat MFA directly. They inherit the result of a legitimate MFA flow.
Info-stealer malware
Many modern malware families are designed to scrape browsers for stored credentials, cookies, and tokens. In practice, this means they are not just stealing usernames and passwords. They are stealing already authenticated states.
That can give the attacker immediate access to email, development platforms, enterprise SaaS tools, and cloud-admin surfaces.
XSS
If a website is vulnerable to cross-site scripting and cookies are not properly protected with HttpOnly, malicious scripts may be able to read and exfiltrate them. That turns a client-side injection flaw into a session compromise.
Malicious or over-permissioned browser extensions
Extensions are often ignored in security conversations, but they can become a direct path into sessions. If an extension can read page content, intercept traffic, or access browser storage in dangerous ways, it may expose authentication artifacts.
Unsecured transport or legacy weaknesses
Plain HTTP, weak internal apps, bad reverse proxies, and poorly designed legacy systems can still expose session data in transit. This is less common than before, but it still matters in older environments and internal tooling.
Physical access to an unlocked device
Not every session attack is advanced. If a browser is open and the user is authenticated, an attacker with device access may not need the password at all. They already have the session in front of them.
Pass-the-Cookie: The Practical Attack Model
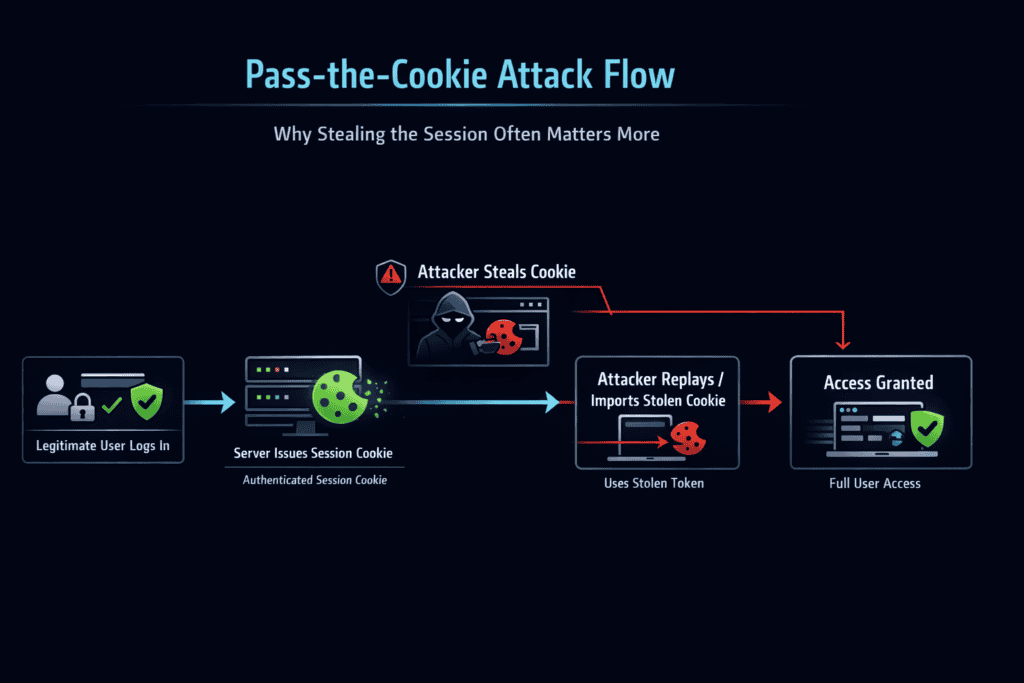
This is why session hijacking and pass-the-cookie attacks are more dangerous than traditional credential theft.
Pass-the-cookie is the simplest way to explain the risk.
The attacker obtains the cookie. Then they replay it.
If the application accepts that cookie as valid, the attacker is treated as the user. They get the same permissions, the same active session context, and the same access level.
This is why the phrase “stealing the password” can be misleading in modern identity incidents. In many cases, the attacker is not stealing identity at the credential layer. They are replaying it at the session layer.
Session Fixation: A Different Route to the Same Outcome
Session theft usually means stealing an already active session. Session fixation is different.
In a session fixation attack, the attacker forces or tricks the victim into using a session ID that the attacker already knows. If the application fails to rotate the session ID after login, the attacker can later reuse that same authenticated session.
The weakness here is not theft after login. It is bad session lifecycle management during login.
A secure application must issue a fresh session after successful authentication. If it does not, it risks turning an unauthenticated session into an authenticated one that the attacker can predict or control.
Session Prediction: When the Session ID Itself Is Weak
Some systems fail even earlier.
If session IDs are predictable, low-entropy, sequential, timestamp-based, or built from guessable values, attackers may be able to predict valid sessions without stealing or fixing them first. This is session prediction.
This is mostly a legacy or custom-implementation problem now, but it still matters in badly designed applications. Strong session management depends on randomness. If the token is guessable, the whole model collapses.
Why Defending the Session Is Harder Than People Think
Developers and defenders do have controls available, but none of them are perfect on their own.
OWASP Session Management Cheat Sheet
Microsoft identity security guidance
HttpOnly
This helps prevent JavaScript from reading cookies. It is critical against some XSS-based theft paths. But it does not stop every kind of session abuse, and it does nothing against malware already running on the endpoint.
Secure
This ensures cookies are only sent over HTTPS. It is necessary, but it does not protect a session once the endpoint itself is compromised.
SameSite
This reduces some cross-site abuse patterns, especially around CSRF. It is useful, but it is not a complete defense against cookie theft or token replay from the user’s own environment.
Short session lifetime
Reducing session duration limits attacker dwell time, but it also creates friction for users. Most organizations compromise here, and attackers benefit from that tradeoff.
Reauthentication for sensitive actions
This is one of the better controls. Even if the session exists, the application can demand fresh proof before allowing high-risk actions such as password changes, payment updates, admin role changes, or privileged operations.
Device and risk binding
Some platforms bind sessions to device posture, browser characteristics, IP signals, or conditional access policies. These controls can reduce replay success, but they need careful tuning because legitimate users move, roam, and change networks constantly.
This complexity further explains why session cookies matter more than your password in modern attack scenarios.
What Users Can Do
Users cannot solve session security alone, but they can reduce exposure.
Log out of sensitive accounts when you are done, especially on shared or semi-trusted devices. Keep browsers updated. Avoid random extensions. Treat extension permissions seriously. Use reputable endpoint protection. Be cautious with phishing links even if they appear to support MFA. Review active sessions on major platforms and revoke sessions you do not recognize.
The important mental shift is this: do not think only about protecting the password. Think about protecting the live authenticated browser.
What Organizations Need To Change
Organizations need to stop treating “MFA enabled” as the end of the identity story.
A stronger model includes:
- session-aware detection
- stronger endpoint security against info-stealers
- phishing-resistant authentication where possible
- reauthentication for sensitive actions
- shorter token lifetime for privileged access
- conditional access and risk-based session controls
- secure cookie configuration
- session revocation and visibility for users and admins
- testing for fixation, prediction, replay, and token handling flaws
In other words, identity security has to extend beyond the login page.
The Real Bottom Line
Why session cookies matter more than your password comes down to one uncomfortable fact: once a session is active, the application usually trusts the session more than the credentials that created it.
That is why attackers increasingly go after cookies, tokens, and authenticated browser state. It is faster than cracking passwords, often bypasses MFA, and can look like perfectly normal user activity.
The password opens the door.
The session decides who the system believes is already inside.
Conclusion
The traditional model of account security starts with credentials. The modern attack model starts after credentials.
This is ultimately why session cookies matter more than your password in modern cybersecurity.
That is the shift many teams still underestimate.
If you only protect the login, but fail to protect the session, you are securing the entrance while leaving the occupied building exposed. Session cookies are not a minor implementation detail. They are the operational trust layer of the modern web.
That is why session cookies matter more than your password in day-to-day account security, incident response, and modern identity defense.
Want to understand how modern identity attacks really work beyond passwords and MFA?
Read these next:
- Why MFA Doesn’t Stop Phishing
- What Is AiTM Phishing and Why It Bypasses MFA
- Session vs Credential Theft
- How Conditional Access Shrinks the Damage of Identity Attacks
If you are building a security strategy in 2026, start by asking a harder question:
What happens after login?
