How Cyber Attacks Happen
A premium educational pillar on the real logic of cyber attacks: how attackers move from reconnaissance to access, from access to persistence, and from single weaknesses to full system compromise.
How Cyber Attacks Happen Is Usually Explained Too Late
Most people encounter cyber attacks only at the moment of visible damage. They hear about the ransomware screen, the stolen credentials, the fraudulent payment, or the leaked data. By that stage the event appears sudden, technical, and almost mysterious. But cyber attacks do not begin where the damage becomes visible. They begin much earlier, often quietly, through reconnaissance, weak processes, trust exploitation, and unnoticed access.
That is why the question is not only what is a cyber attack, but how cyber attacks happen in practice. Once you shift from the visible incident to the hidden sequence behind it, the subject becomes much clearer. Attackers gather information, locate the easiest entry point, exploit access, establish persistence, and then execute the real objective. The mechanics vary, but the structure repeats.
This article treats cyber attacks as a system rather than a cinematic event. That shift matters because the same system logic appears again and again across phishing, credential theft, ransomware, insider misuse, and supply chain compromise. If you understand the structure, you are no longer only reacting to outcomes. You start seeing the conditions that make those outcomes likely.
Cyber attacks do not succeed because every attacker is brilliant. They succeed because many systems remain predictable, overloaded, and easier to manipulate than the people inside them realize.
Why Modern Systems Invite Attack
Modern society runs on digital dependence. Communication, finance, healthcare, logistics, energy, education, and governance all rely on interconnected systems. That dependence creates extraordinary efficiency, but it also creates concentration of risk. Once processes, identities, transactions, and records become digital, they become available for manipulation at scale.
The result is a world in which a single weak credential, exposed portal, or successful phishing email can trigger consequences far beyond the original point of entry. This is why cybersecurity cannot be reduced to antivirus software or technical hardening alone. It is a structural issue involving infrastructure, identity, human behavior, process design, and organizational discipline.
This broader logic connects directly to earlier Darja Rihla systems articles. If you have not yet read What Is a Complex System?, Feedback Loops in Systems, Emergence in Complex Systems, and The Hidden Logic of Complex Systems, this pillar extends that cluster into cybersecurity.
Cluster bridge: Cyber attacks are best understood as system events. They move through dependencies, exploit behavior, reinforce success patterns, and create cascading effects. That is why cybersecurity belongs inside systems thinking, not outside it.
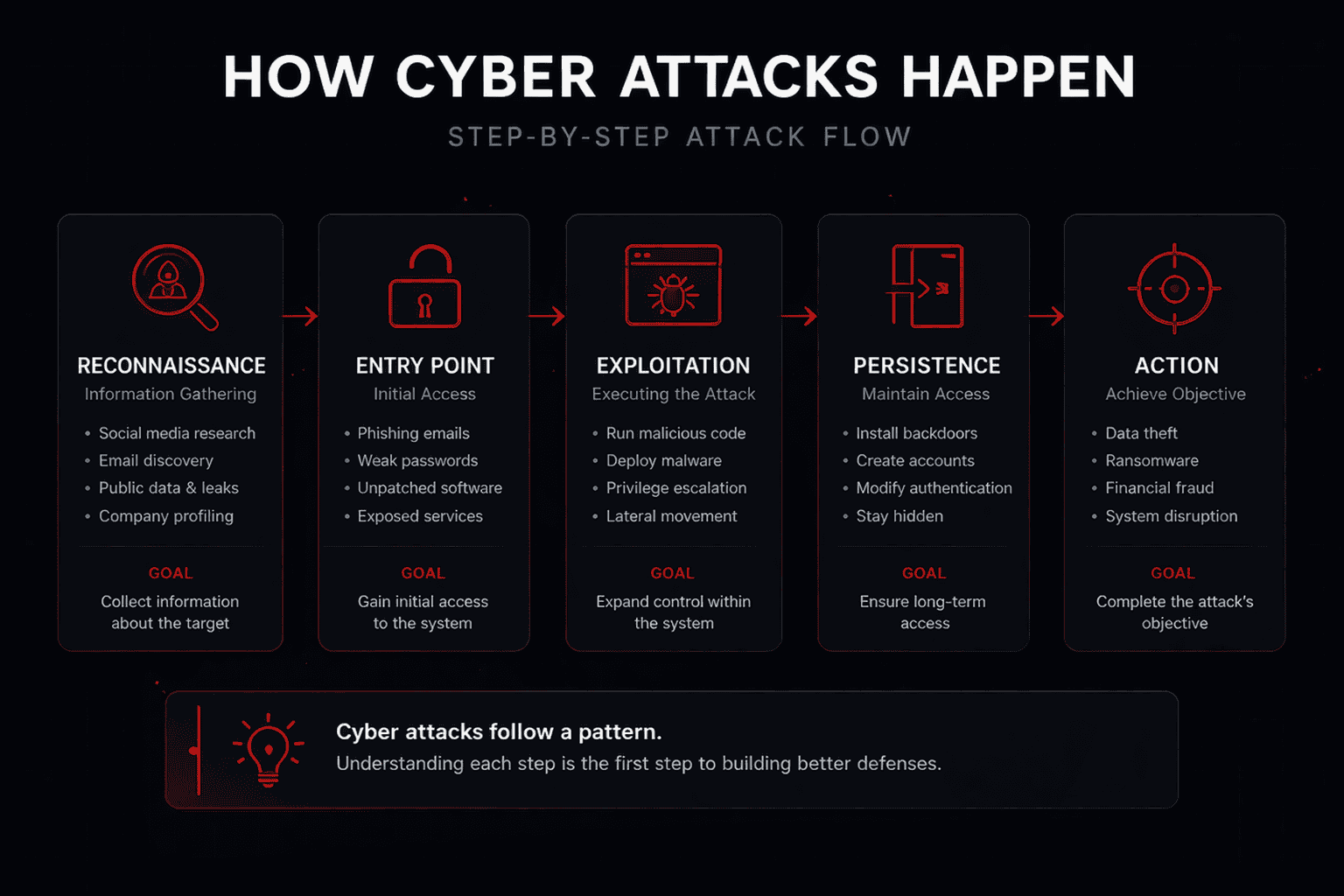
The Five-Part Logic of a Cyber Attack
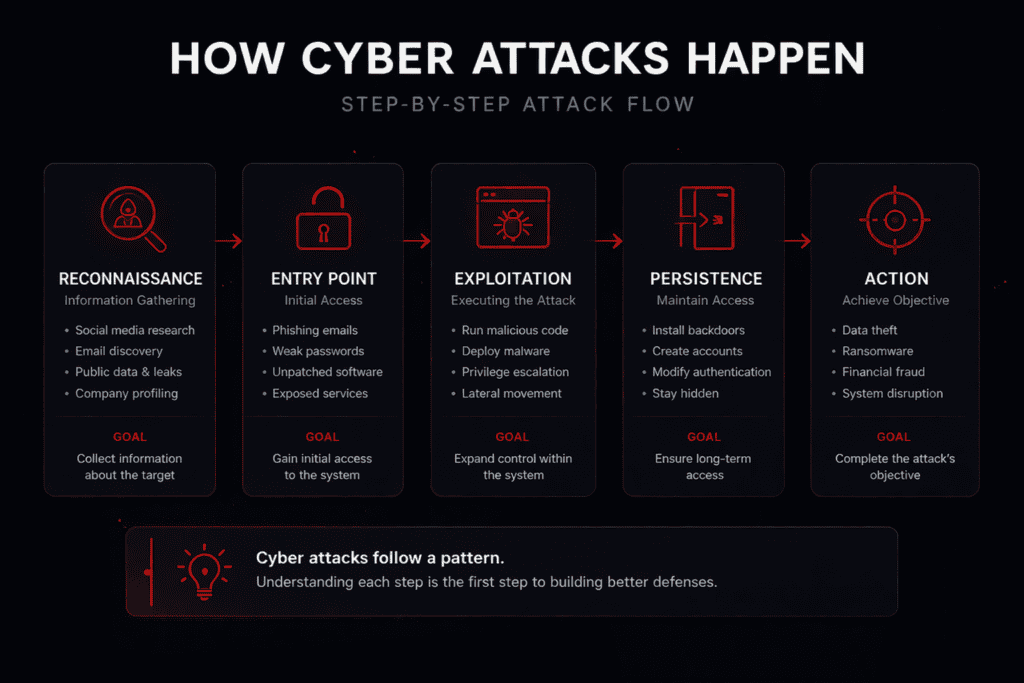
Most cyber attacks are easiest to understand when broken into five phases. In reality, attackers may skip, combine, or repeat some of them. But as a teaching framework, these five phases explain how cyber attacks happen across many real-world cases.
Reconnaissance
Information gathering on people, systems, technologies, suppliers, and exposed surfaces.
Initial Access
Entry through phishing, weak passwords, exposed services, or unpatched software.
Exploitation
Using the foothold to execute code, expand privileges, and move further inside.
Persistence
Creating ways to stay inside or return later even if part of the attack is detected.
Objective
Data theft, fraud, surveillance, ransomware, or disruption.
1. Reconnaissance
Every serious cyber attack starts with information. Attackers rarely move blindly. They gather names from LinkedIn, infer internal email patterns, identify external suppliers, scan websites, inspect exposed services, search public breach dumps, and study the technologies an organization uses. The point of reconnaissance is not drama. It is reduction of uncertainty.
2. Initial Access
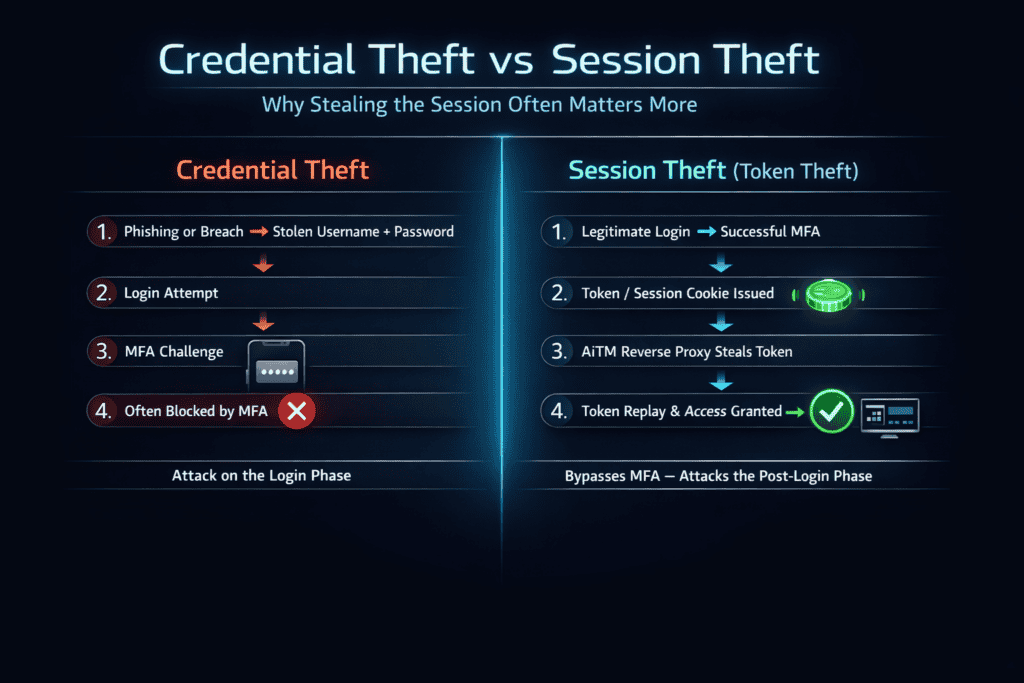
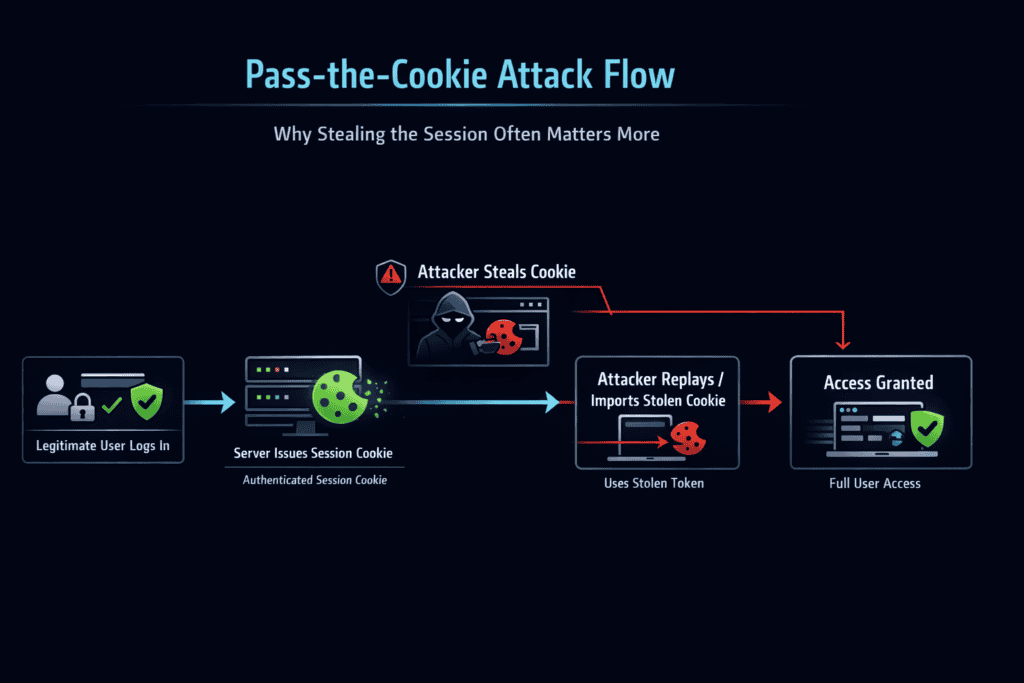
This is the moment most people imagine as the start of the attack, but it is already the result of earlier preparation. Initial access usually comes through a familiar weakness: a phishing email, a weak or reused password, an unpatched system, a leaked token, an exposed remote service, or a misconfigured cloud interface.
3. Exploitation
Once attackers gain entry, they try to turn presence into capability. This can mean running malicious code, extracting secrets from memory, abusing legitimate tools, moving laterally, or escalating privileges.
4. Persistence
Temporary access is useful. Durable access is far more valuable. Attackers often create persistence by installing backdoors, generating hidden accounts, abusing scheduled tasks, planting web shells, or modifying authentication paths.
5. Final Objective
Only at the last phase does the attacker execute the visible goal: encrypting systems for ransom, stealing customer data, extracting payment flows, committing fraud, or silently maintaining surveillance.
How systems fail under pressure
Read How Cybersecurity Shapes the Modern World for the larger civilizational context behind digital dependence and fragility.
Attack model reference
For an external framework reference, see MITRE ATT&CK, which catalogs attacker tactics and techniques across real intrusions.
The Big Myth: Cyber Attacks Are Always Extremely Advanced
The popular narrative says attackers are mostly elite technical geniuses who defeat strong systems through extraordinary skill. Sometimes that is true. But as a general public explanation, it is misleading. Most cyber attacks do not need the most advanced path. They only need the path of least resistance.
Weak passwords, reused credentials, ignored updates, over-privileged accounts, poor monitoring, and users placed under time pressure are often enough. This is why cyber attacks feel sophisticated after the fact, but often depend on surprisingly ordinary weaknesses during the process.
Why People Still Open the Door
Human behavior remains central to how cyber attacks happen. Attackers exploit trust, habit, urgency, fatigue, and routine. A finance employee in a hurry does not experience a fake invoice request as an abstract security problem. They experience it as a work task arriving at the wrong moment.
This is why the phrase “humans are the weakest link” is too shallow. People are not simply a defective layer attached to otherwise perfect systems. They are embedded actors inside systems that often demand more sustained vigilance than real work environments can support.

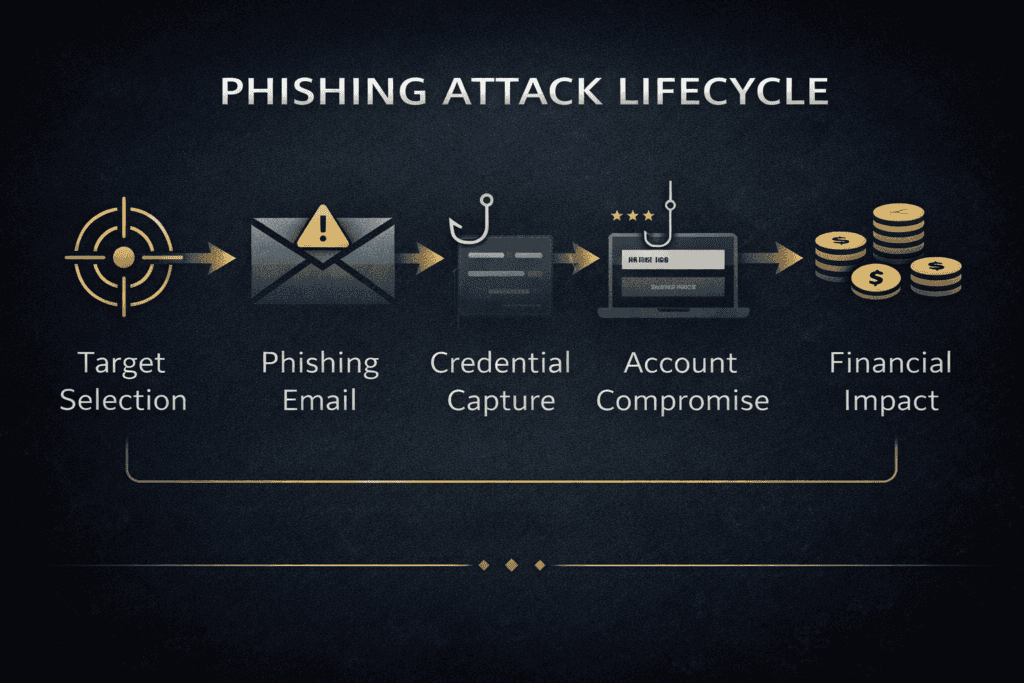
Why Small Weaknesses Scale Into Large Incidents
Cyber attacks behave like system events because digital environments are deeply interconnected. One stolen credential can expose multiple services. One compromised update can affect thousands of endpoints. One unmonitored identity can become the bridge between internal trust zones. In these environments, small failures do not remain isolated. They propagate.
That is why cyber defense is strongest when it breaks chains early. Attackers rely on sequence. Good defense interrupts sequence.
Cascading compromise
Phishing becomes credential theft. Credential theft becomes lateral movement. Lateral movement becomes ransomware or fraud.
Chain interruption
MFA, strong monitoring, segmentation, fast patching, and low-friction reporting break the attack before it matures.
How to Defend Without Becoming a Specialist
You do not need elite technical skill to reduce cyber risk. You need better security habits and better system design. The core educational move is to stop treating defense as a bag of tools and start treating it as a repeatable behavior system.
- Use a password manager so every important account has a unique password.
- Enable multi-factor authentication on email, financial, and administrative accounts.
- Keep systems updated and patch exposed services early.
- Pause before urgent requests, especially payment, credential, or login requests.
- Verify through a second channel when a message feels unusual, rushed, or powerful.
- Report suspicious emails and prompts rather than silently deleting them.
- Treat digital trust as something to check, not something to assume.
Cybersecurity Flashcards
Compact flashcards, like the earlier Darja Rihla pages, rebuilt in a button-based layout so they do not dominate the page. Use them as a quick revision layer under the pillar.
What is the first phase in how cyber attacks happen?
What Most People Still Get Wrong
Most people try to defend against cyber attacks by focusing only on tools. They ask what software to buy, what app to install, or what platform to trust. But tools are only one layer. If behavior is weak, responsibilities are unclear, and systems are designed badly, even expensive tools fail.
The deeper defense comes from structure: identity hygiene, verification habits, better defaults, reduced privilege, good monitoring, realistic training, and a culture in which secure behavior is practical rather than theatrical.
The Clear Position
My position is that cyber attacks should be taught first as structured processes inside vulnerable systems, not first as isolated technical events. That framing is more accurate, more educational, and more useful. It explains why phishing still works, why weak identities still matter, why small failures escalate, and why defense is strongest when it interrupts attack chains early.