Introduction
Conditional Access reduces identity attack damage by shifting security from a one-time login check to continuous validation.
Modern attackers do not break in. They log in.
Using techniques such as AiTM phishing, token theft, and session hijacking, they bypass MFA and operate inside your environment as legitimate users.
That means the real battle starts after authentication.
Conditional Access, combined with Continuous Access Evaluation (CAE) and Token Protection, transforms identity security into a system that limits how long an attacker can stay and how much damage they can do.
Table of Contents
Why Identity Attacks Now Focus on Sessions
Attackers have shifted from stealing passwords to stealing sessions and tokens.
Related concept: Session Hijacking
Once a user logs in, systems rely on tokens instead of rechecking credentials. If an attacker steals that token, they inherit access instantly.
This is why AiTM phishing works:
- MFA is completed legitimately
- Token is captured
- Session is reused
- No further authentication required
The password becomes irrelevant.
How Conditional Access Reduces Identity Attack Damage
Conditional Access reduces identity attack damage by continuously validating context.
Implemented through Microsoft Entra ID, it evaluates:
- Identity
- Device
- Location
- Risk
- Behavior
Instead of granting full trust after login, it enforces conditional trust at every step.
The Core Mechanism: From Login to Continuous Validation
Conditional Access does not simply operate as a linear post-login control. In a technically accurate Zero Trust model, policy evaluation happens before access is fully granted.
The diagram below illustrates how Conditional Access and Continuous Access Evaluation work together in a Zero Trust model.
Rather than granting permanent trust after login, the system continuously reassesses the session based on identity, context, and risk signals.
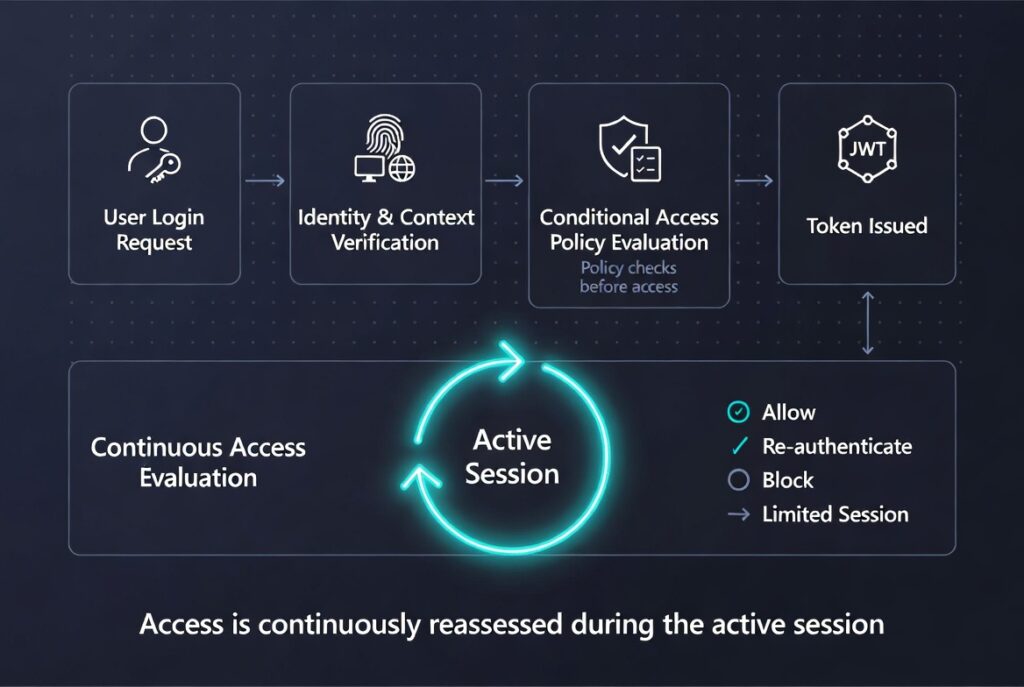
The flow starts with the user login request and proceeds through identity and context verification before Conditional Access policies are evaluated.
Only after these checks pass is the token issued and the session activated.
From that point onward, Continuous Access Evaluation continuously reassesses the active session and can dynamically allow, challenge, block, or restrict access.
The correct enterprise flow is:
1. User Login Request
2. Identity Verification
3. Conditional Access Policy Evaluation
4. Token Issuance
5. Session Activation
6. Continuous Access Evaluation (ongoing loop)
7. Session Decision
This means access is not trusted by default after authentication.
Before the access token is issued, Microsoft Entra ID evaluates critical policy conditions such as:
– MFA requirement
– device compliance
– trusted location
– risk signals
– user role sensitivity
– application sensitivity
Only if these conditions are satisfied is the token issued and the session activated.
After the session starts, Continuous Access Evaluation acts as an ongoing validation loop rather than a separate linear step.
This is a core Zero Trust principle:
trust is temporary and continuously reassessed.
Key Control Layer
Token Protection Explained
Token Protection cryptographically binds tokens to a specific device.
This means:
- stolen tokens are significantly harder to reuse
- replay attacks from external systems are blocked
- token portability is reduced
Limitations:
- less effective against same-device attacks
- browser session hijacking remains possible
- support depends on client and application
It increases attacker effort and reduces token portability.

Continuous Access Evaluation (CAE) Explained
Continuous Access Evaluation introduces near real-time control.
Triggers include:
- Password change
- Risk detection
- Location change
- Account disablement
Instead of waiting for token expiration, access can be revoked quickly.
This turns sessions into unstable environments for attackers.
Why Continuous Evaluation Is a Loop, Not a Step
Continuous Access Evaluation should not be visualized as a one-time stage after Conditional Access.
Technically, it functions as an event-driven feedback loop during the active session.
Risk events such as:
– password reset
– account disablement
– impossible travel
– IP location change
– sign-in risk increase
– device posture change
can immediately trigger a re-evaluation of session trust.
This can result in:
– session continuation
– forced re-authentication
– limited access
– immediate session revocation
In Zero Trust architecture, every request can change the trust level of the session.
Real-World Attack Scenario
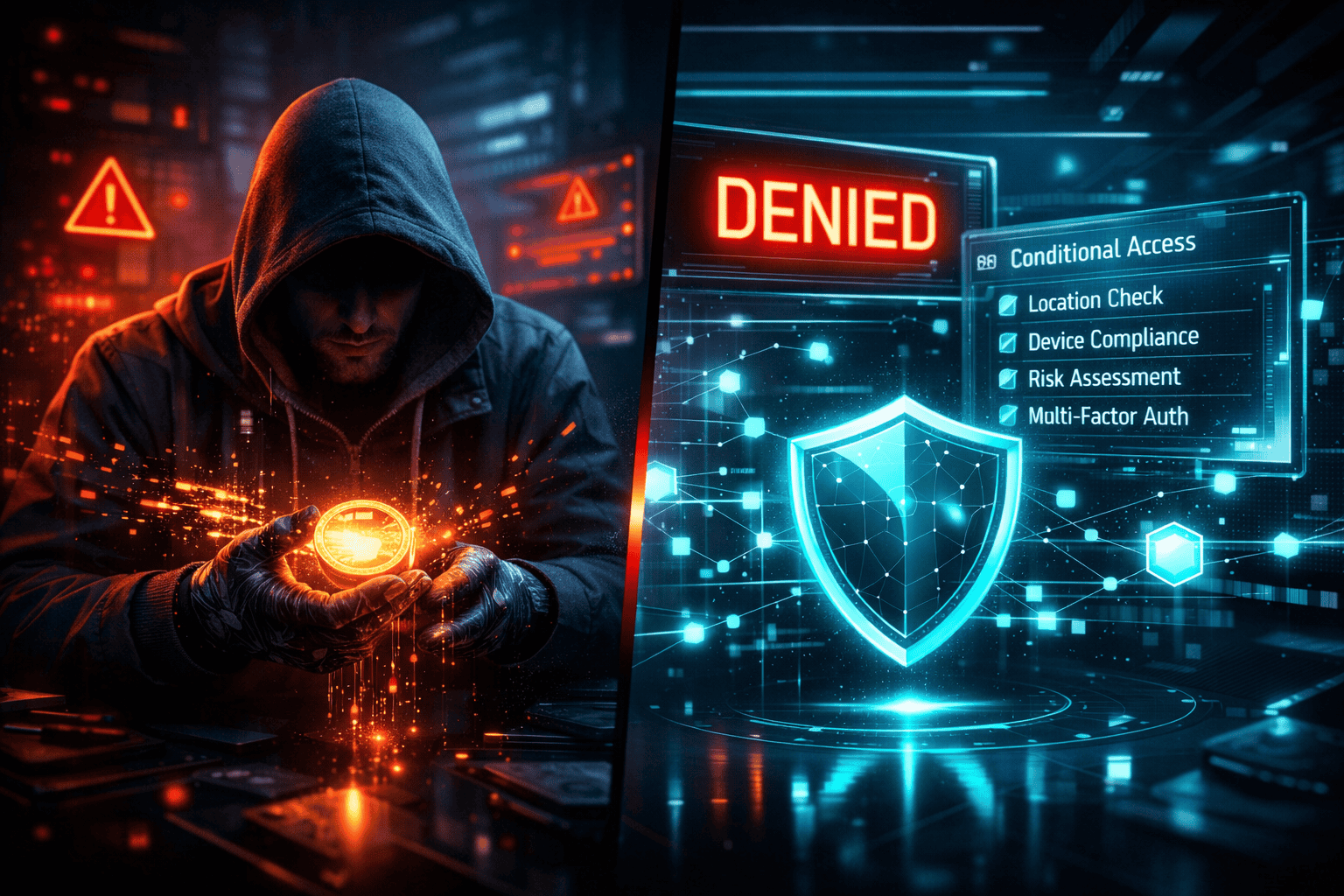
Without Conditional Access
- Token stolen
- Attacker logs in silently
- Session remains valid
- Data is accessed and exfiltrated
Result: full compromise
With Conditional Access
- Unknown device blocked
- Suspicious location triggers re-auth
- Risk triggers session termination
- Token replay fails
Result: limited damage
7 Critical Conditional Access Policies
- Block legacy authentication
- Require MFA for all users
- Enforce device compliance
- Restrict access by location
- Enable risk-based policies
- Limit session lifetime
- Require phishing-resistant MFA for admins
These controls directly reduce attacker dwell time and limit post-login damage.
Why MFA Alone Fails
MFA protects the login event.
It does not protect:
- Session reuse
- Token theft
- Post-authentication actions
Conditional Access replaces static trust with dynamic validation.
Implementation Strategy
1. Enforce MFA and block legacy authentication
2. Add device compliance and location policies
3. Enable CAE and risk-based access
4. Implement Token Protection
5. Simulate attacks and optimize policies
Final Insight
Identity security does not fail at the login moment. It fails when trust becomes static after access is granted.
Conditional Access enforces trust before token issuance.
Continuous Access Evaluation ensures that trust remains dynamic throughout the active session.
Security is therefore not a one-time authentication event.
It is a continuous trust lifecycle.
Test Your Identity Security Before Attackers Do
Most environments are secure at login but vulnerable after authentication.
I help organizations identify:
– token theft exposure
– weak Conditional Access configurations
– session control gaps
– Zero Trust policy weaknesses
Book a Conditional Access Security Audit and discover how long an attacker could remain inside your environment.
Related Articles
- Pillar: How Cyber Attacks Happen
- Supporting
- Phishing Attack Explained
- Why MFA Doesn’t Stop Phishing
- Session vs Credential Theft
- Why Session Cookies Matter More Than Your Password
Next in This Series
Session vs Credential Theft: Why attackers now prefer stealing active sessions instead of passwords, and what this means for Zero Trust security.
Leave a Reply