🪝 The Reality Most People Still Don’t See: Phishing Attack Explained
Most people misunderstand how a phishing attack works.
Modern phishing attacks are no longer about suspicious emails: They are structured systems designed to exploit trust, identity, and workflow.
“Check the sender.”
“Don’t click suspicious links.”
“Look for spelling mistakes.”
That advice belongs to 2012.
Modern phishing doesn’t look suspicious.
It looks like work.
And that changes everything.
Key Insight
Phishing is not about emails.
It is about how attackers exploit trust to gain access to systems, identities, and money.
Table of Contents
The Core Shift: From Fake Emails to Fake Workflows
Phishing used to be about deception.
Today, it’s about simulation.
Attackers no longer try to trick you with obvious scams.
They recreate:
- internal processes
- real communication patterns
- trusted platforms
- decision-making moments
This is called:
Workflow Mimicry
A phishing attack succeeds when it feels like a normal task.
Not when it looks real,
but when it behaves real.
The Phishing System (The Phishing Attack System Explained)
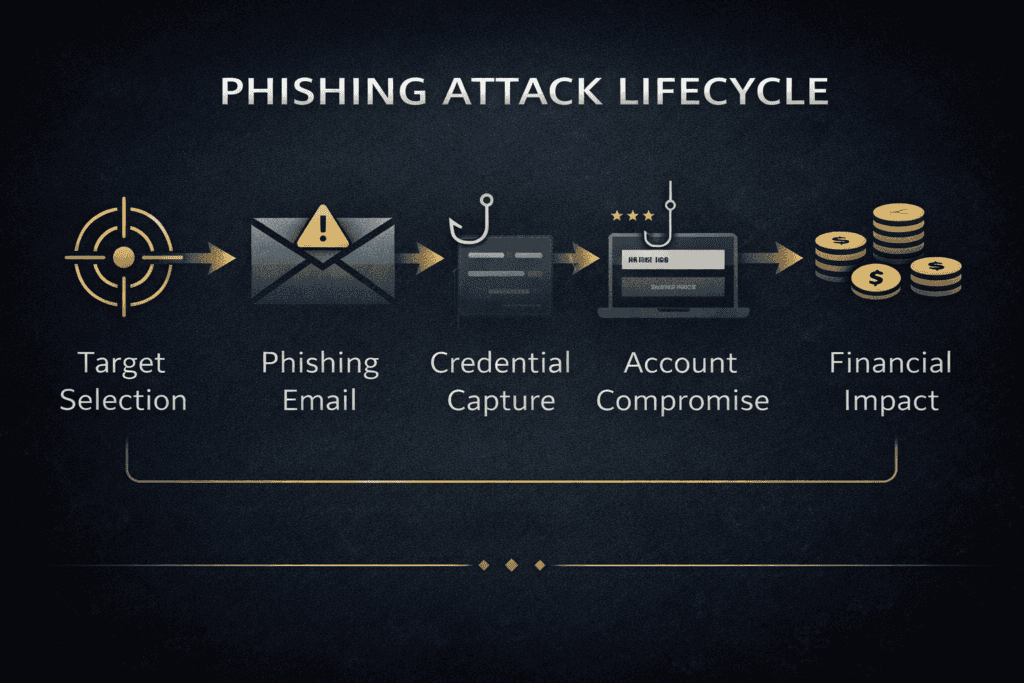
A phishing attack explained in simple terms shows how attackers move from trust to access without breaking systems.
Forget the idea of “a phishing email.”
Phishing is a multi-layer system designed to convert trust into access.
SYSTEM FLOW
Target Selection
→ Context Mapping
→ Narrative Engineering
→ Infrastructure Setup
→ Delivery
→ Interaction
→ Identity Capture
→ Account Takeover
→ Persistence
→ Internal Exploitation
→ Monetization
Layer 1: Narrative Engineering (The Real Weapon)
The strongest phishing attacks are not technical.
They are contextual.
They answer one question:
“What would this person realistically do right now?”
Examples:
- Finance → “Invoice needs approval today”
- HR → “Updated contract document”
- Employee → “Your session expired, re-login”
- Manager → “Quick approval needed before meeting”
Insight
Attackers don’t break systems.
They enter systems by behaving like them.
Layer 2: Infrastructure (The Invisible Engine)
Behind every phishing attack is a modular ecosystem.
Attackers don’t build attacks.
They assemble them.
Common components:
- phishing kits (ready-made login pages)
- reverse proxies (session interception)
- compromised websites (hosting)
- lookalike domains
- cloud abuse (legit platforms)
- residential proxies (stealth)
Insight
Phishing is not hacking.
It is logistics + psychology + infrastructure.
Layer 3: Identity Capture (Where It Actually Happens)
This is where most people misunderstand phishing.
It’s not about stealing passwords anymore.
It’s about capturing:
- credentials
- session cookies
- authentication tokens
- OAuth permissions
The New Reality
Identity is the new perimeter
Attackers don’t need your system.
They need to become you.
Why MFA Alone Is Not Enough
Many organizations think MFA solved phishing.
It didn’t.
Modern attacks use:
- Adversary-in-the-Middle (AiTM)
- token theft
- session hijacking
- OAuth consent abuse
Result:
The attacker logs in with your session, not your password.
Insight
Security that protects login
but not session
is incomplete.
Layer 4: Post-Compromise (Where Damage Happens)
Phishing is just the entry point.
The real attack starts after access.
What attackers do next:
- read emails for context
- set inbox rules (hide messages)
- monitor financial communication
- impersonate internally
- expand access to other users
The Most Common Outcome
Business Email Compromise (BEC)
Not malware.
Not ransomware.
Just:
- trust
- timing
- manipulation
Layer 5: Monetization (The Endgame)
Phishing is not about access.
It’s about value extraction.
Outcomes:
- fraudulent payments
- selling access
- data theft
- ransomware staging
- long-term espionage
Brutal Truth
Phishing is lead generation for cybercrime.
Why Smart People Still Fall for Phishing
According to CISA, phishing remains one of the most common initial access methods in cyber attacks.
This is where most explanations fail.
Phishing does not target stupidity.
It targets human operating conditions.
Psychological Triggers
Phishing is also closely linked to human behavior and decision-making under pressure.
Authority
Looks like Microsoft, your boss, or finance.
Urgency
“Today.” “Now.” “Action required.”
Familiarity
Real logos, real platforms, real workflows.
Cognitive Load
You are busy. That’s enough.
Process Compliance
You are trained to act on requests.
Insight
Phishing works because it aligns with how work actually happens.
Why Most Organizations Defend This Wrong
Typical defenses:
- awareness training
- email filtering
- warning banners
These help, but they miss the core issue.
The Real Problem
Phishing is not an email issue.
It is a:
Trust + Identity + Process problem
What Real Defense Looks Like
This phishing attack explained demonstrates that modern attacks focus on identity, not just emails.
You don’t fix phishing at one layer.
You break the system.
Defense by Layer
Before Delivery
- SPF / DKIM / DMARC
- domain monitoring
- filtering
During Interaction
- browser isolation
- safe link analysis
- reporting channels
Identity Layer
- phishing-resistant MFA
- conditional access
- token protection
- OAuth governance
After Compromise
- detect abnormal inbox rules
- session revocation
- token invalidation
- anomaly detection
Insight
Prevention is not enough.
Detection and response define survival.
Where Phishing Fits in the Bigger Picture
Phishing is often the first step in a much larger attack chain.
To understand how attackers move from initial access to full system compromise, read:
The Strategic Reality
Phishing succeeds because organizations optimize for:
- speed
- usability
- efficiency
Not verification.
Final Insight
Phishing is not an email attack.
It is a system designed to convert trust into access.
Related Articles
- How Cyber Attacks Actually Happen
- Human Error in Cybersecurity
- How to Build Personal Systems That Actually Work
Want to Go Deeper?
Understanding how a phishing attack works is step one.
But protecting yourself requires the right tools and systems.
🔐 Essential Security Tools
1. Password Manager (Critical Layer)
If attackers target identity, your first defense is strong credential management.
Recommended:
👉 Use a password manager to:
- generate strong passwords
- prevent reuse
- protect against credential stuffing
2. Multi-Factor Authentication (MFA Apps)
Passwords alone are not enough.
Recommended:
👉 Always enable MFA on:
- email accounts
- banking
- cloud platforms
3. Phishing Protection & Browsing Security
Modern phishing often happens inside the browser.
Recommended:
- Malwarebytes Browser Guard
- uBlock Origin (ad + tracker blocking)
- Brave Browser (privacy-first)
👉 These help:
- block malicious domains
- reduce exposure to phishing pages
4. Endpoint Security (Device Protection)
If malware is involved, your device becomes the entry point.
Recommended:
- Malwarebytes
- Bitdefender
- Windows Defender (baseline, but configure it properly)
5. Email Security Awareness (Behavior Layer)
No tool replaces awareness, but systems help.
Recommended:
- KnowBe4 (training platform)
- Proofpoint (enterprise-level)
👉 For individuals:
- create your own “pause rule” before clicking anything urgent
6. Identity Monitoring (Advanced Layer)
Because phishing often leads to identity compromise.
Recommended:
- Have I Been Pwned (free check)
- Identity Guard / Aura (premium monitoring)
Leave a Reply